ECDSA256V-IP Core Datasheet

|
Core Facts |
|
|
Provided with Core |
|
|
Documentation |
User Guide, Design Guide |
|
Design File Formats |
Encrypted File |
|
Instantiation Templates |
VHDL |
|
Reference Designs & Application Notes |
Vivado Project, See Reference design manual |
|
Additional Items |
Demo on KR260 board |
|
Support |
|
|
Support Provided by Design Gateway Co., Ltd. |
|
Design Gateway Co., Ltd
E-mail: ip-sales@design-gateway.com
URL: design-gateway.com
Features
· Pure hardware ECDSA signature verification with no CPU, software or external memory required
· Support NIST P-256 curve with 256-bit message digest
· Over 100 operation per second @240 MHz
· Compliant with FIPS 186-4 standard
· Support for other curves available on request
Table 1 Table Description
|
Family |
Example Device |
Fmax (MHz)
|
CLB Regs
|
CLB LUTs
|
CLB1 |
DSP |
BRAMTile |
Design Tools |
|
Zynq-Ultrascale+ |
xck26-sfvc784-2LV-c |
240 |
14038 |
12367 |
2314 |
22 |
9 |
Vivado2022.1 |
Notes:
1) The actual logic resource depends on the percentage of unrelated logic.
General Description
The Elliptic Curve Digital Signature Algorithm (ECDSA) is a public-key cryptographic algorithm widely used for authentication and secure communication. It provides strong security with relatively small key sizes, making it efficient for applications such as SSL/TLS certificates, secure web transactions, and digital signatures in embedded or IoT systems. ECDSA is standardized in FIPS 186-4, Digital Signature Standard (DSS) and ANSI X9.62-2005, Public Key Cryptography for the Financial Services Industry.
The ECDSA256V IP Core is a pure hardware accelerator designed specifically for verifying ECDSA signatures. It supports the NIST P-256(*) curve with a 256-bit message digest, enabling high-performance and low-latency signature verification without requiring a CPU, software stack, or external memory. By offloading verification from the processor, the ECDSA256V-IP is ideal for security-critical applications where both performance and reliability are essential.
To ensure data integrity, the verifier first passes the received message though a hash function to create a 256-bit digest. The ECDSA256V-IP then uses this digest together with the sender’s public key and the received signature to perform verification. All elliptic-curve and cryptographic operations are handled internally by the IP core, which outputs a simple result: VALID if the signature matches the message, or INVALID if the data has been altered. This process is illustrated in Figure 1.
Note: (*) Equivalent curve names for NIST P-256:
· SECG: secp256r1
· ANSI X9.62: prime256v1
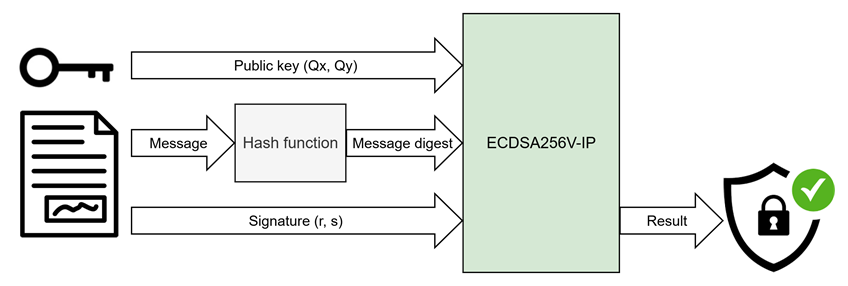
Figure 1 ECDSA256V-IP use case
Functional Description
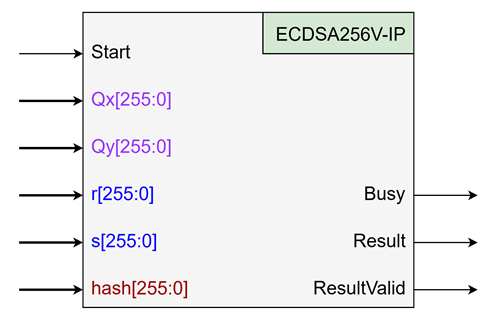
Figure 2 ECDSA256V-IP interface
Table 2 User I/O Signals
|
Signal name |
Dir |
Description |
|
RstB |
In |
IP core system reset. Active low. |
|
Clk |
In |
IP core system clock. |
|
version[31:0] |
Out |
32-bit version number of IP |
|
Control Signal |
||
|
Start |
In |
Asserted for 1 clock cycle to Initiate ECDSA verification. All ECDSA parameters must be valid when this signal is asserted. |
|
Busy |
Out |
Indicates the IP core is processing verification. Busy is asserted after Start is active. |
|
ResultValid |
Out |
Indicates that the verification result is available. |
|
Result |
Out |
Verification result: 0 = Invalid (message does NOT match signature) 1 = Valid (message matches signature) |
|
ECDSA parameters |
||
|
Qx[255:0] |
In |
x-coordinate of the public key, little-endian. |
|
Qy[255:0] |
In |
y-coordinate of the public key, little-endian. |
|
r[255:0] |
In |
r component of the ECDSA signature, little-endian. |
|
s[255:0] |
In |
s component of the ECDSA signature, little-endian. |
|
hash[255:0] |
In |
Message digest, little endian. |
The operation of the ECDSA256V-IP core can be completed in three simple steps:
1. Set the ECDSA parameters.
2. Assert the Start signal.
3. Read the verification result.
To verify an ECDSA signature, the following parameters are required: public key (Qx, Qy), signature (r, s), and message digest (hash). Since the ECDSA256V-IP supports the NIST P-256 curve, each input is 256 bits in length and represented in little-endian format.
All parameters must valid when the Start signal is asserted. While the Busy status is active, the IP core executes the verification process. Once verification is complete, Busy is de-asserted and ResultValid is asserted, indicating that the verification result is available, as shown in Figure 3.
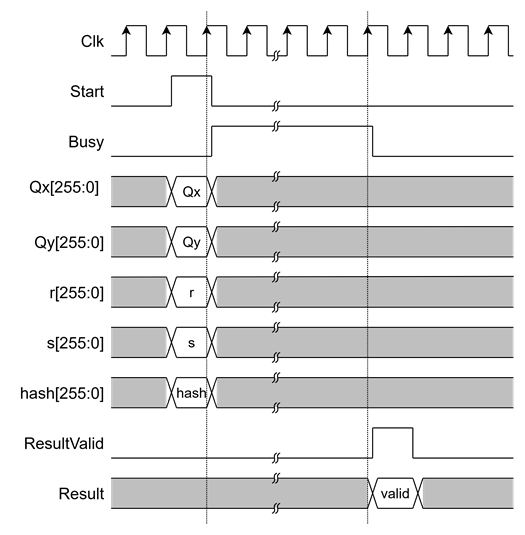
Figure 3 ECDSA256V-IP interface timing diagram
Verification Methods
The ECDSA256V-IP Core functionality was verified by simulation and also proved on real board design by using KR260 Evaluation Board.
Recommended Design Experience
The user must be familiar with HDL design methodology to integrate this IP into a system.
Ordering Information
This product is available directly from Design Gateway Co., Ltd. Please contact Design Gateway Co., Ltd. For pricing and additional information about this product, use the contact information on the front page of this datasheet.
Revision History
|
Revision |
Date (D-M-Y) |
Description |
|
1.00 |
10-Oct-25 |
Initial release |